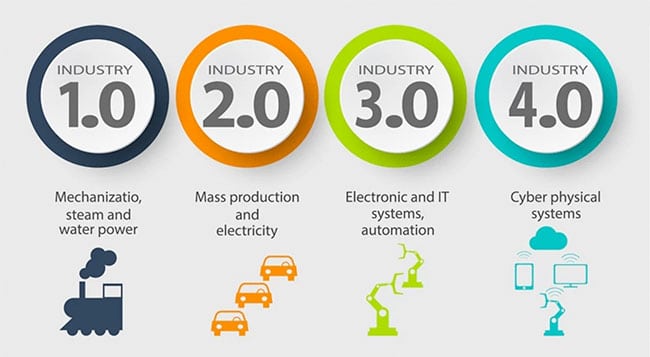
In previous blog posts, we discussed technologies like IoT, RPA and AI, also known as Industry 4.0. These technologies come with their demands of data, storage and power, and their challenges are not exempted. Recently, ENISA published ‘Good practices for Security of Internet of Things in the context of Smart Manufacturing’ to support businesses in handling the security challenges that arise when using these technologies. Also, national and international laws and regulations are created, or coming to oblige technology to comply to high security and privacy standards (like GDPR and the planned IoT cybersecurity law in the US). So, what can we expect from this good practice?
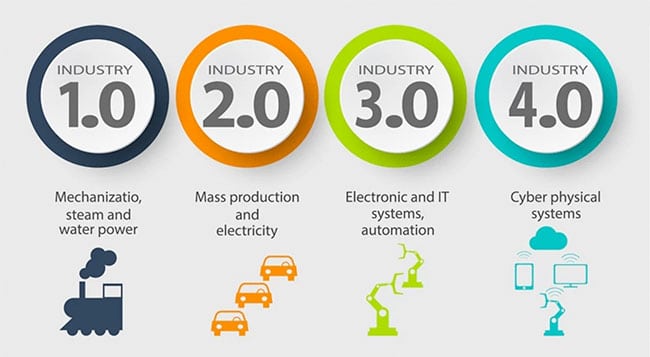
The good practice of ENISA identifies threats and relates them to assets and security measures since the proper method is also based on a review of a wide range of standards, schemes and initiatives (like resources from ISO, NIST and SANS Institute). A link with the GDPR is also made. Therefore, this document can be seen as a guide in risk analysis and a checklist of process steps for companies that use Industry 4.0 and Smart Manufacturing technologies. The structure described in performing a risk assessment is pretty basic. However, the security measures and examples mentioned here help you to have a better understanding of the assets, possible cyber security attacks and risks that should be taken into account.
The good practice by ENISA cannot be seen as a rulebook that prescribed all measures that need to be implemented to be sure your IoT environment is adequately secured. The document must support a wide range of companies and technologies; therefore, the security measures can be seen as considerations that must be taken into account when setting up the analysis. For compliance with multiple frameworks and standards, a mapping is available with a variety of standards and frameworks. Due to the use of a wide range of resources, the security measures will be probably used and equal to coming law and legislation, as we have seen at the introduction of the GDPR.
The good practice relies on the ‘Baseline Security Recommendation for IoT’, and therefore it has similarities with that study also provided by ENISA. Although a lot of the content relies on the Baseline, the good practice is beneficial and more mature for using it to set up or review your current environment.
Datacenter.com complies to strict physical regulations like PCI DSS, ISO 27001, ISO 9001 and is audited periodically by independent certified auditors. Using transparent assurance reports like ISAE 3402 our security measures can be linked to your security needs.